ATHR Vishing-as-a-Service: AI Voice Scams Go Plug and Play

Cybercrime Just Got a SaaS Business Model
Security researchers have uncovered a new criminal toolkit that packages every stage of a voice phishing attack into a single, browser-based platform. Known as ATHR, the service combines AI-generated phone calls, phishing emails, credential harvesting pages, and a live campaign dashboard into what amounts to vishing-as-a-service.
The platform is being sold on cybercrime forums for $4,000 upfront plus 10% of any profits generated, according to researchers at Abnormal Security who analyzed the kit in detail. For that price, a single operator can run large-scale phone scams against customers of Google, Microsoft, Coinbase, Binance, Yahoo, AOL, and other widely used services, all from a browser tab.
This is the moment social engineering stopped being a skilled craft and started becoming scalable infrastructure. And for defenders, it changes the threat model in ways that email filters alone cannot address.
How ATHR Works: The TOAD Attack Chain
ATHR is built around a technique called telephone-oriented attack delivery, or TOAD. Unlike traditional phishing, which relies on malicious links or infected attachments, TOAD attacks flip the model on its head.
Here's the typical flow:
- The lure email arrives — The victim receives what looks like a legitimate security alert or account notification. Crucially, it contains no links and no attachments — just a phone number for the recipient to call.
- The victim initiates contact — Because the victim dials the number themselves, the psychological framing shifts. They believe they are contacting a trusted institution, which lowers their guard significantly.
- The AI voice agent takes over — A scripted AI agent answers the call, walks the victim through a fake security scenario, and guides them toward entering credentials on a phishing page, installing remote-access software, or reading out a multi-factor authentication code.
- The operator watches in real time — A live dashboard lets the attacker see exactly what the victim is doing on the phishing site, redirect them between pages, and capture credentials the instant they are submitted.
“The lure email contains a phone number, not a malicious URL,” Abnormal Security noted in its report. “There are no payloads to detonate and no suspicious domains to blocklist.” That simple design choice is what makes TOAD campaigns so difficult for conventional security tools to catch.
Why This Changes the Threat Model
Historically, voice phishing campaigns required trained human operators. A scammer had to sound convincing, handle objections, improvise when victims asked awkward questions, and manage the pacing of a live conversation. That human constraint limited how many calls could be run in parallel and how quickly criminal crews could scale.
ATHR removes the constraint.
One Operator, Many Campaigns
The platform runs on the open-source Asterisk telephony engine and uses WebRTC to handle calls directly through a web browser, no plugins or specialized hardware required. A single person can now manage phishing email delivery, multiple simultaneous voice calls, credential harvesting, and campaign analytics from one interface.
“This is what separates ATHR from earlier callback infrastructure,” Abnormal wrote. “Previous platforms required trained human callers. ATHR automates the entire interaction, allowing a single operator to run campaigns across multiple brands simultaneously without scaling headcount.”
AI Voice Agents That Sound Human
The AI agents built into ATHR follow scripted scenarios that mimic legitimate security workflows. They confirm suspicious account activity, walk victims through fabricated “account recovery” steps, and eventually request six-digit verification codes. Because the scripts are refined and the voices are AI-generated, victims are interacting with a system that sounds professional, calm, and authoritative.
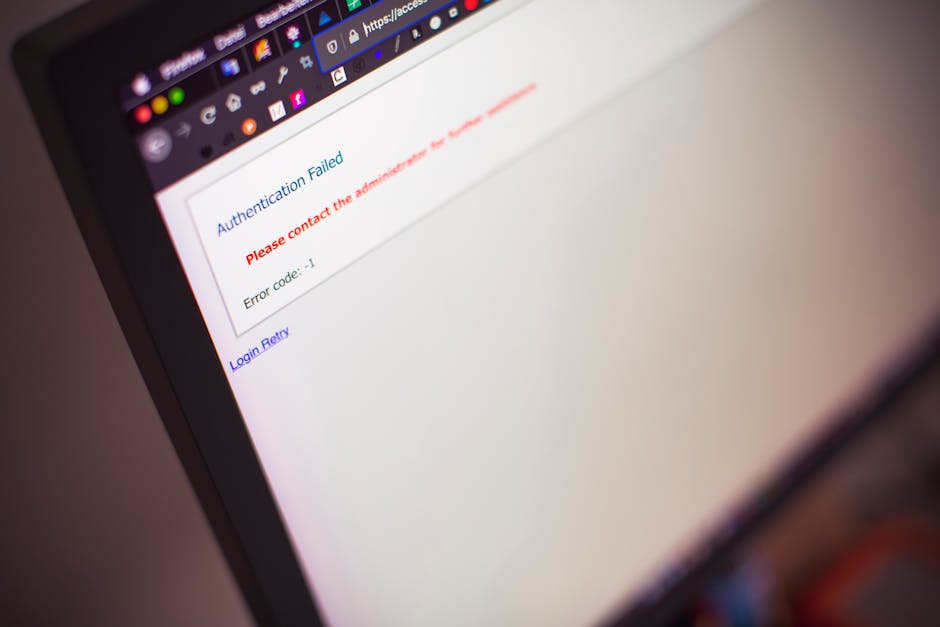
Synchronized Voice and Phishing Pages
ATHR includes phishing panels that replicate the login flows of Coinbase, Binance, Google, Microsoft, Yahoo, and AOL. During a call, the AI voice agent and the phishing website work in concert. As the victim is instructed to “log in to verify your identity,” the operator can watch their progress live, redirect them to the right fake page, and capture usernames, passwords, and MFA codes the moment they are submitted.
Rapid A/B Testing of Lures
The dashboard also gives operators the kind of campaign optimization tools you would expect from a legitimate marketing platform. As Abnormal Security researchers put it in their report: “An operator who sees a low callback rate can adjust the lure template, change the sender profile, or refine the personalization fields, and then immediately observe whether the next batch of emails generates more calls.”
The Commoditization of Social Engineering
ATHR is not an isolated development. It is the latest expression of a broader trend: the commoditization of advanced cybercrime tooling. What used to require bespoke infrastructure, custom code, and skilled operators is now being packaged and sold like a SaaS product, complete with pricing tiers, support channels, and revenue sharing.
Lucy Finlay, director of secure behavior and analytics at Redflags, described the shift bluntly: “What we are seeing is the complete commercialization of social engineering. The moment you remove that constraint and replace it with an AI voice agent, you’re no longer dealing with targeted scams — you’re dealing with scalable infrastructure for mass manipulation.”
Real-time vishing kits have already been linked to major breaches. In January 2026, Okta reported that tooling allegedly used by ShinyHunters was deployed in an operation targeting SoundCloud, Betterment, and Crunchbase, alongside attempted attacks on Okta, Microsoft, and Google. Okta reserved full indicators of compromise for paying customers, underscoring how quickly this class of threat has moved from niche to mainstream.
Why Your Existing Defenses May Not Catch This
Most organizations have invested heavily in email security, endpoint detection, and network monitoring. Those controls remain essential, but ATHR-style campaigns are engineered to slip past them.
- No malicious links — The lure email contains only a phone number, so URL reputation engines and safe-browsing tools have nothing to analyze.
- No attachments — There is no payload for endpoint protection or sandboxing to detect.
- Legitimate infrastructure — Asterisk and WebRTC are the same technologies used by legitimate contact centers worldwide, making call traffic difficult to block on reputation alone.
- Victim-initiated contact — Because the victim dials the number, there is no inbound signal for network security tools to inspect.
- Real-time credential capture — Even if a phishing domain is eventually blocklisted, the credentials have usually already been harvested and used.
The decisive control point is the human on the phone. If that person recognizes the behavioral pattern of a vishing attack, the entire chain collapses. If they do not, no downstream technology can meaningfully intervene.
What Vishing Resilience Actually Looks Like
Training employees to defend against AI-powered voice scams requires more than a once-a-year compliance video. It requires teaching specific, recognizable behaviors that are effective regardless of how convincing the attacker sounds.
Rule 1: Never Trust a Phone Number From an Email
If an email asks the recipient to call a number to resolve a security issue, the correct response is to ignore that number entirely. Employees should navigate to the service’s official website or mobile app and use the contact information published there. This single habit neutralizes the entire TOAD attack chain.
Rule 2: Never Read Verification Codes Over the Phone
Legitimate security teams will never ask for a multi-factor authentication code, one-time password, or recovery code during a phone call. Any request to “confirm” a six-digit number verbally is a red flag, regardless of how plausible the rest of the conversation sounds.
Rule 3: Treat Urgency as a Warning Sign
AI voice agents are scripted to create pressure — your account will be locked, a fraudulent transaction must be reversed, your identity must be verified immediately. Employees should be trained to recognize urgency as an engineered tactic and respond by slowing down, not speeding up.
Rule 4: Report Suspicious Calls, Not Just Emails
Many organizations have a “report phish” button in Outlook or Gmail but no clear process for reporting a suspicious phone call. That gap means vishing attempts often go unreported, leaving security teams blind to active campaigns targeting their workforce.
Rule 5: Assume the Voice Is Fake
AI voice synthesis has advanced to the point where even deliberate red flags — odd pacing, unnatural intonation — can no longer be relied on. Employees should be trained to evaluate calls based on what is being asked, not how the caller sounds.
How empowsec Helps Build Vishing Resilience
The threats employees face have expanded well beyond the inbox, and security awareness training needs to keep pace. empowsec is designed to prepare workforces for exactly the kind of multi-channel, data-enriched social engineering attacks that platforms like ATHR enable.
- Realistic phishing simulations that mirror modern lure patterns, including callback-style emails designed to test whether employees dial numbers they should not.
- Targeted training modules on vishing, voice deepfakes, callback phishing, and the specific tactics being used in live attack campaigns right now.
- Immediate, contextual debriefs when an employee falls for a simulated attack, explaining exactly what they missed and how the real-world equivalent would have played out.
- Behavioral analytics that give security leaders visibility into which teams, roles, and regions are most vulnerable to specific attack types, so training investment can follow risk.
- Continuous reinforcement through short, regular exercises that build the kind of instinctive caution that a single annual training cannot produce.
For small businesses, the same platform delivers enterprise-grade training without the enterprise complexity, turning security awareness into a practical operational control rather than a compliance checkbox.
Immediate Steps for Security Leaders
- Brief your workforce on TOAD — Make sure employees understand that a phishing email no longer has to contain a link to be dangerous. A phone number is now a payload.
- Establish a vishing reporting channel — Create a clear, easy-to-remember process for employees to report suspicious phone calls, ideally in the same system they already use for phishing emails.
- Run a callback-style phishing simulation — Test whether employees will dial a number provided in an email under the pressure of a fabricated security alert. The results will tell you where your exposure is concentrated.
- Reinforce MFA code discipline — Remind every employee, in writing, that no legitimate support process will ever ask for an MFA code verbally or via chat.
- Prioritize finance and privileged users — Operators of platforms like ATHR target high-value accounts first. Finance teams, executive assistants, and IT administrators should receive more frequent, more realistic simulations than general staff.
- Track trends, not just incidents — Vishing campaigns evolve quickly. Security awareness programs need continuous content updates so training reflects the tactics employees will actually encounter.
Key Takeaways
ATHR is a preview of where social engineering is heading. When AI voice agents, real-time credential harvesting, and browser-based telephony are bundled into a $4,000 product, the barrier to running sophisticated phone scams collapses. Here is what matters for defenders:
- Vishing is no longer labor-constrained — AI voice agents let a single operator run campaigns at scale, across multiple brands, with no human callers required.
- TOAD attacks bypass traditional email defenses — A lure with nothing but a phone number gives security tools nothing to analyze. The human on the call becomes the only meaningful control.
- Commoditization accelerates everything — When advanced tooling is sold as a subscription, the volume and sophistication of attacks rise faster than most organizations can adapt.
- Awareness training must expand beyond email — Employees need specific, practiced rules for phone calls, messaging apps, and voice interactions, not just inbox hygiene.
- Simulation is how behavioral change sticks — Reading about vishing builds awareness. Experiencing a realistic simulation builds the reflex that actually stops the attack.
The attackers have industrialized voice fraud. The most effective response is an equally systematic approach to preparing the humans they are trying to manipulate. With empowsec, enterprises and small businesses can give their workforce the realistic practice and immediate feedback required to keep pace with threats that evolve as quickly as ATHR does.