Why Most Phishing Simulations Fail — And How to Fix Yours

The Click Rate Trap
Every quarter, you send out a phishing simulation. Every quarter, the click rate drops a little. Your CISO presents the trend line to the board, everyone nods approvingly, and the security awareness program gets a green checkmark.
Then a real phishing email lands, and someone in accounting wires $47,000 to a fraudulent vendor.
This scenario plays out more often than most organizations admit. The problem isn't that phishing simulations don't work — it's that most programs are designed to produce good metrics rather than genuine behavioral change. Here are the five most common mistakes and how to fix each one.
1. You're Testing Recognition, Not Response
Most simulations measure a single binary outcome: did the employee click or not? But in the real world, the correct response to a suspicious email isn't just "don't click." It's report it.
An employee who ignores a phishing email and an employee who reports it look identical in your click rate data. But the reporter just gave your SOC team early warning about an active campaign. The ignorer gave you nothing.
Fix: Track your report rate alongside your click rate. A mature program should see reporting rates climb above 60%, meaning the majority of employees who spot something suspicious take the extra step of flagging it. If your organization uses a report phishing button in your email client, measure how many simulated phishing emails get reported — not just how many don't get clicked.
2. Your Simulations Are Too Obvious
If every simulation uses broken English, Nigerian prince narratives, or obviously fake domains, your employees learn to spot your simulations — not real phishing attacks.
Modern phishing campaigns are sophisticated. They use legitimate-looking domains, proper grammar, and contextually relevant pretexts. Business email compromise (BEC) attacks often contain zero malicious links — just a polite request from someone impersonating a known colleague.
Fix: Calibrate simulation difficulty to your organization's maturity. Use a mix of difficulties:
- Easy (20% of simulations): Obvious red flags — misspellings, urgency, suspicious domains. These build baseline confidence.
- Medium (50%): Realistic pretexts using your industry context — vendor payment requests, HR policy updates, IT password resets.
- Hard (30%): Spear-phishing caliber — personalized, no obvious red flags, using domains that closely mimic real services your company uses.
If your click rate on hard simulations is below 5%, your employees aren't learning — your simulations aren't challenging enough.
3. You're Shaming Instead of Teaching
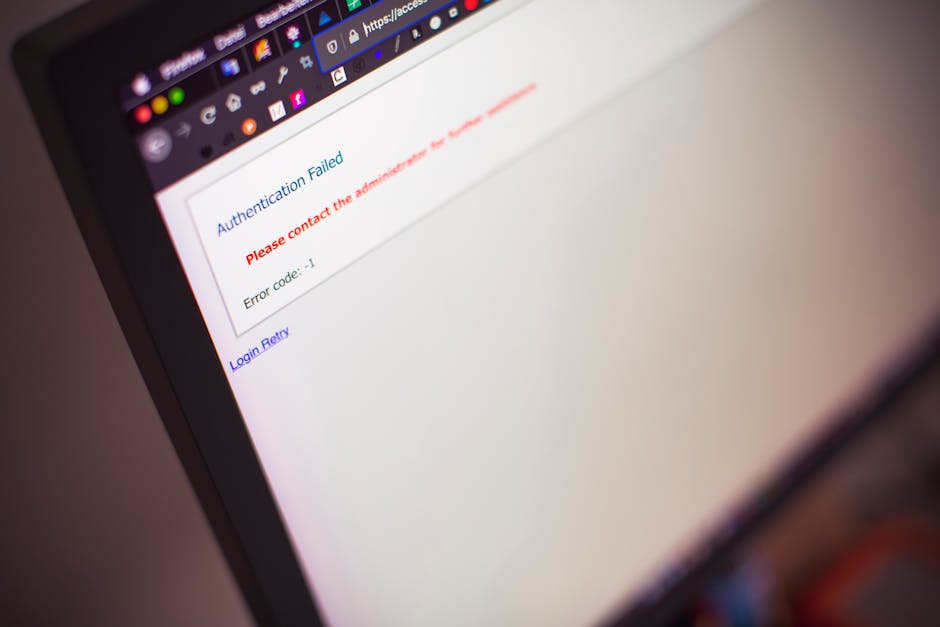
Nothing kills a security culture faster than the "gotcha" moment. An employee clicks a simulated phishing link, and a screen appears saying: "You failed! You just compromised the company."
Research from the National Institute of Standards and Technology (NIST) consistently shows that punitive approaches to security awareness reduce reporting behavior. Employees who fear punishment learn to hide mistakes rather than flag them — exactly the opposite of what you need during a real incident.
Fix: Replace the shame page with an immediate learning moment. When someone clicks, show them:
- Which specific red flags were present in the email
- What the correct action would have been
- A 60-second micro-training reinforcing the concept
Frame it as practice, not punishment. Pilots use flight simulators to practice emergency responses — nobody calls them failures when the simulated engine fails. Your phishing simulations should work the same way.
4. You Simulate Too Rarely
Quarterly phishing tests are the security awareness equivalent of cramming for an exam. Employees briefly heighten their awareness around the expected test window, then revert to autopilot.
The forgetting curve is real. Research by Hermann Ebbinghaus demonstrated that people forget approximately 70% of new information within 24 hours without reinforcement. A single simulation every 90 days provides almost zero lasting behavioral impact.
Fix: Move to continuous simulation — at least monthly, ideally with randomized timing so employees can't predict the next test. Each employee should receive simulations at different intervals, using different templates and difficulty levels.
This approach offers two advantages:
- It keeps awareness consistently elevated rather than creating temporary spikes
- It generates enough data points to identify which employees, departments, or attack types need targeted intervention
5. You're Not Closing the Loop
Most simulation programs follow a rigid cycle: send simulation, collect data, generate report, repeat. But the data collected rarely influences what happens next.
If 40% of your finance team clicked a vendor payment simulation, does that trigger targeted training for the finance team? Does it change the types of simulations they receive? Does anyone check whether the same individuals keep clicking?
Fix: Build adaptive training paths that respond to simulation results:
- Repeat clickers get additional micro-training modules and more frequent simulations
- Departments with high click rates on specific pretexts receive targeted campaigns addressing their risk profile
- Consistent reporters get recognized (publicly or privately) to reinforce the behavior
- Risk scores that aggregate simulation performance, training completion, and reporting behavior into a single metric per user
The goal is a feedback loop where simulation data drives training decisions, and training outcomes are measured by subsequent simulation performance.
What Good Looks Like
A mature phishing simulation program doesn't optimize for a low click rate. It optimizes for organizational resilience — the ability to detect, report, and respond to phishing attacks before damage occurs.
Here's what the metrics look like for organizations that get this right:
- Click rate: Below 5% on medium-difficulty simulations
- Report rate: Above 60% of all simulated emails get reported
- Time to report: Median under 5 minutes from delivery
- Repeat click rate: Less than 2% of employees click on two or more consecutive simulations
- Training completion: Above 95% within SLA
These metrics tell a story that click rate alone cannot: your employees don't just avoid phishing emails — they actively defend the organization against them.
Key Takeaways
If your phishing simulation program feels like a checkbox exercise, it probably is. Here's how to make it meaningful:
- Measure reporting, not just clicking — the report rate is your most important metric
- Calibrate difficulty to challenge employees, not just confirm they can spot the obvious
- Teach, don't shame — immediate learning moments outperform punitive approaches
- Simulate continuously — monthly minimum, randomized timing
- Close the feedback loop — let simulation data drive adaptive training paths
Phishing simulations are the closest thing your organization has to a live-fire security exercise. Treat them like training, not testing, and the results will follow.